- If applicable, pay an application fee. Does not need to complete a knowledge or vision test, unless indicated on the DL record. Does not need to complete a drive test, unless indicated on the DL record. California law does not allow for an ID card to be issued to individuals who are not legally present in the United States.
- Go to the NVidia drivers download page here; In the manual search section, select your graphic card type (e.g. GeForce), select your graphics card series (e.g. Series 900 if your graphics card is between 900 – 999 or select series 10 if your card is 1080, 1020 etc.).
Open the device manager and expand display or the ports drivers. Double click the driver you recently updated to open the driver properties and switch to the “Driver” tab. Click the “Roll Back Driver” button. This will restore the driver to the previous working condition. Fixes an issue that prevents administrators from importing drivers into Configuration Manager. The problem concerns a newer signing method that isn't supported without first installing this hotfix.
Applies to: Windows 10
If you run into problems when using Windows Update, start with the following steps:
Run the built-in Windows Update troubleshooter to fix common issues. Navigate to Settings > Update & Security > Troubleshoot > Windows Update.
Install the most recent Servicing Stack Update (SSU) that matches your version of Windows from the Microsoft Update Catalog. See Servicing stack updates for more details on servicing stack updates.
Make sure that you install the latest Windows updates, cumulative updates, and rollup updates. To verify the update status, refer to the appropriate update history for your system:
Advanced users can also refer to the log generated by Windows Update for further investigation.
You might encounter the following scenarios when using Windows Update.
Why am I offered an older update?
The update that is offered to a device depends on several factors. The following are some of the most common attributes:
- OS Build
- OS Branch
- OS Locale
- OS Architecture
- Device update management configuration
If the update you're offered isn't the most current available, it might be because your device is being managed by a WSUS server, and you're being offered the updates available on that server. It's also possible, if your device is part of a deployment group, that your admin is intentionally slowing the rollout of updates. Since the deployment is slow and measured to begin with, all devices will not receive the update on the same day.
My device is frozen at scan. Why?
The Settings UI communicates with the Update Orchestrator service that in turn communicates with to Windows Update service. If these services stop unexpectedly, then you might see this behavior. In such cases, follow these steps:
Close the Settings app and reopen it.
Start Services.msc and check if the following services are running:
- Update State Orchestrator
- Windows Update
Feature updates are not being offered while other updates are
Devices running Windows 10, version 1709 through Windows 10, version 1803 that are configured to update from Windows Update (including Windows Update for Business) are able to install servicing and definition updates but are never offered feature updates.
Checking the WindowsUpdate.log reveals the following error:
The 0x80070426 error code translates to:
Microsoft Account Sign In Assistant (MSA or wlidsvc) is the service in question. The DCAT Flighting service (ServiceId: 855E8A7C-ECB4-4CA3-B045-1DFA50104289) relies on MSA to get the global device ID for the device. Without the MSA service running, the global device ID won't be generated and sent by the client and the search for feature updates never completes successfully.
To resolve this issue, reset the MSA service to the default StartType of 'manual.'

Issues related to HTTP/Proxy
Windows Update uses WinHttp with Partial Range requests (RFC 7233) to download updates and applications from Windows Update servers or on-premises WSUS servers. Therefore proxy servers on the network must support HTTP RANGE requests. If a proxy was configured in Internet Explorer (User level) but not in WinHTTP (System level), connections to Windows Update will fail.
To fix this issue, configure a proxy in WinHTTP by using the following netsh command:
Note
You can also import the proxy settings from Internet Explorer by using the following command: netsh winhttp import proxy source=ie
If downloads through a proxy server fail with a 0x80d05001 DO_E_HTTP_BLOCKSIZE_MISMATCH error, or if you notice high CPU usage while updates are downloading, check the proxy configuration to permit HTTP RANGE requests to run.
You might choose to apply a rule to permit HTTP RANGE requests for the following URLs:
*.download.windowsupdate.com*.dl.delivery.mp.microsoft.com*.delivery.mp.microsoft.com
If you can't allow RANGE requests, you'll be downloading more content than needed in updates (as delta patching will not work).
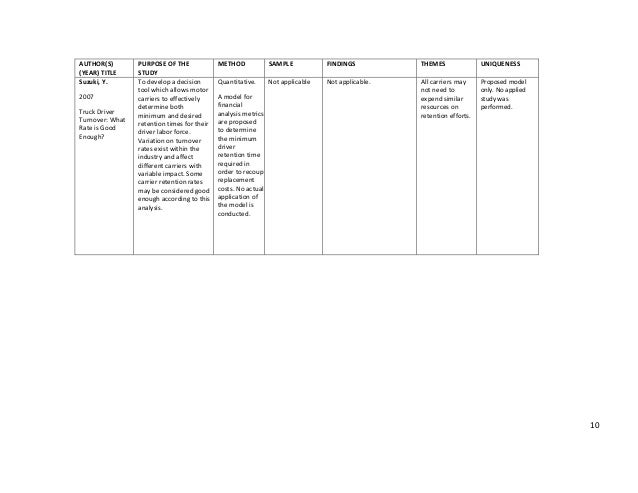
The update is not applicable to your computer
The most common reasons for this error are described in the following table:

| Cause | Explanation | Resolution |
|---|---|---|
| Update is superseded | As updates for a component are released, the updated component will supersede an older component that is already on the system. When this occurs, the previous update is marked as superseded. If the update that you're trying to install already has a newer version of the payload on your system, you might receive this error message. | Check that the package that you are installing contains newer versions of the binaries. Or, check that the package is superseded by another new package. |
| Update is already installed | If the update that you're trying to install was previously installed, for example, by another update that carried the same payload, you may encounter this error message. | Verify that the package that you are trying to install was not previously installed. |
| Wrong update for architecture | Updates are published by CPU architecture. If the update that you're trying to install does not match the architecture for your CPU, you may encounter this error message. | Verify that the package that you're trying to install matches the Windows version that you are using. The Windows version information can be found in the 'Applies To' section of the article for each update. For example, Windows Server 2012-only updates cannot be installed on Windows Server 2012 R2-based computers. Also, verify that the package that you are installing matches the processor architecture of the Windows version that you are using. For example, an x86-based update cannot be installed on x64-based installations of Windows. |
| Missing prerequisite update | Some updates require a prerequisite update before they can be applied to a system. If you are missing a prerequisite update, you may encounter this error message. For example, KB 2919355 must be installed on Windows 8.1 and Windows Server 2012 R2 computers before many of the updates that were released after April 2014 can be installed. | Check the related articles about the package in the Microsoft Knowledge Base (KB) to make sure that you have the prerequisite updates installed. For example, if you encounter the error message on Windows 8.1 or Windows Server 2012 R2, you may have to install the April 2014 update 2919355 as a prerequisite and one or more pre-requisite servicing updates (KB 2919442 and KB 3173424). To determine if these prerequisite updates are installed, run the following PowerShell command: get-hotfix KB3173424,KB2919355, KB2919442. If the updates are installed, the command will return the installed date in the InstalledOn section of the output. |
Issues related to firewall configuration
Error that you might see in Windows Update logs:
Or
Or
Go to Services.msc and ensure that Windows Firewall Service is enabled. Stopping the service associated with Windows Firewall with Advanced Security is not supported by Microsoft. For more information, see I need to disable Windows Firewall.
Issues arising from configuration of conflicting policies
Windows Update provides a wide range configuration policy to control the behavior of the Windows Update service in a managed environment. While these policies let you configure the settings at a granular level, misconfiguration or setting conflicting policies may lead to unexpected behaviors.
For more information, see How to configure automatic updates by using Group Policy or registry settings for more information.
Device cannot access update files
Ensure that devices can reach necessary Windows Update endpoints through the firewall. For example, for Windows 10, version 2004, the following protocols must be able to reach these respective endpoints:
| Protocol | Endpoint URL |
|---|---|
| TLS 1.2 | *.prod.do.dsp.mp.microsoft.com |
| HTTP | emdl.ws.microsoft.com |
| HTTP | *.dl.delivery.mp.microsoft.com |
| HTTP | *.windowsupdate.com |
| HTTPS | *.delivery.mp.microsoft.com |
| TLS 1.2 | *.update.microsoft.com |
| TLS 1.2 | tsfe.trafficshaping.dsp.mp.microsoft.com |
Note
Be sure not to use HTTPS for those endpoints that specify HTTP, and vice versa. The connection will fail.
The specific endpoints can vary between Windows 10 versions. See, for example, Windows 10 2004 Enterprise connection endpoints. Similar articles for other Windows 10 versions are available in the table of contents nearby.
Updates aren't downloading from the intranet endpoint (WSUS or Configuration Manager)
Windows 10 devices can receive updates from a variety of sources, including Windows Update online, a Windows Server Update Services server, and others. To determine the source of Windows Updates currently being used on a device, follow these steps:
- Start Windows PowerShell as an administrator.
- Run $MUSM = New-Object -ComObject 'Microsoft.Update.ServiceManager'.
- Run $MUSM.Services.
Not Applicable Drivers
Check the output for the Name and OffersWindowsUPdates parameters, which you can interpret according to this table.
| Output | Meaning |
|---|---|
| - Name: Microsoft Update -OffersWindowsUpdates: True | - The update source is Microsoft Update, which means that updates for other Microsoft products besides the operating system could also be delivered. - Indicates that the client is configured to receive updates for all Microsoft Products (Office, etc.) |
| - Name: DCat Flighting Prod - OffersWindowsUpdates: True | - Starting with Windows 10 1709, feature updates are always delivered through the DCAT service. - Indicates that the client is configured to receive feature updates from Windows Update. |
| - Name: Windows Store (DCat Prod) - OffersWindowsUpdates: False | -The update source is Insider Updates for Store Apps. - Indicates that the client will not receive or is not configured to receive these updates. |
| - Name: Windows Server Update Service - OffersWindowsUpdates: True | - The source is a Windows Server Updates Services server. - The client is configured to receive updates from WSUS. |
| - Name: Windows Update - OffersWindowsUpdates: True | - The source is Windows Update. - The client is configured to receive updates from Windows Update Online. |
You have a bad setup in the environment
In this example, per the Group Policy set through registry, the system is configured to use WSUS to download updates (note the second line):
From Windows Update logs:
In the above log snippet, we see that the Criteria = 'IsHidden = 0 AND DeploymentAction=*'. '*' means there is nothing specified from the server. So, the scan happens but there is no direction to download or install to the agent. So it just scans the update and provides the results.

Not Applicable Vertaling
As shown in the following logs, automatic update runs the scan and finds no update approved for it. So it reports there are no updates to install or download. This is due to an incorrect configuration. The WSUS side should approve the updates for Windows Update so that it fetches the updates and installs them at the specified time according to the policy. Since this scenario doesn't include Configuration Manager, there's no way to install unapproved updates. You're expecting the operational insight agent to do the scan and automatically trigger the download and installation but that won’t happen with this configuration.
High bandwidth usage on Windows 10 by Windows Update
Users might see that Windows 10 is consuming all the bandwidth in the different offices under the system context. This behavior is by design. Components that might consume bandwidth expand beyond Windows Update components.
The following group policies can help mitigate this situation:
- Blocking access to Windows Update servers: Policy Turn off access to all Windows Update features (Set to enabled)
- Driver search: Policy Specify search order for device driver source locations (Set to 'Do not search Windows Update')
- Windows Store automatic update: Policy Turn off Automatic Download and Install of updates (Set to enabled)
Other components that connect to the internet:
- Windows Spotlight: Policy Configure Windows spotlight on lock screen (Set to disabled)
- Consumer experiences: Policy Turn off Microsoft consumer experiences (Set to enabled)
- Background traffic from Windows apps: Policy Let Windows apps run in the background
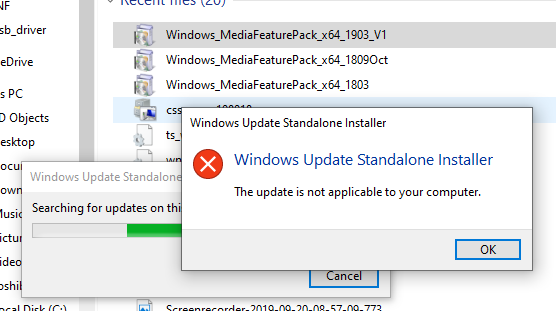
Looking at the INFs they were written in normal Intel fashion and even making some modifications to strip down to Windows 8.1 did nothing. Digging through the SCCM logs was not a ton of help either. AdminUI.Log, DriverCatalog.Log, SMSAdmin.Log, Setupapi.app.log, you name it. All just said the same thing, driver not applicable. Those actually gave an error code of 0x80070661.
Turns out the issue is due to our Site Server being on 2008 R2. Specifically with the OS. The signing in these drivers is using a newer method thats not native in 2008 R2. Microsoft released KB3025419 which states to install KB2837108 and KB2921916 to update the OS to support the newer signing method in ConfigMgr. Coincidentally both this KB and the Toshiba device came out at the same time. After applying the hotfix and restarting (not required but the KB states to do anyway) we are now able to import these newer signed drivers and image the Toshibas up successfully and quickly.
-Kevin
